This post is the third part of a series of blog posts entitled Creating your own OpenID Connect server with ASOS:
- Introduction
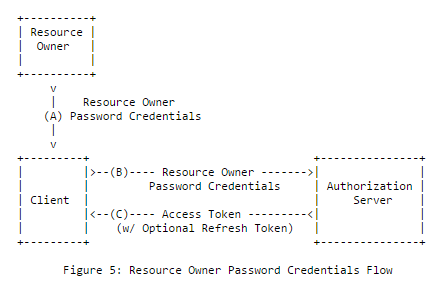
- Choosing the right flow(s)
- Registering the middleware in the ASP.NET Core pipeline
- Creating your own authorization provider
- Implementing the resource owner password credentials grant
- Implementing the authorization code and implicit flows
- Adding custom claims and granting scopes
- Testing your authorization server with Postman
- Conclusion
In the previous post (Choosing the right flow(s)), we saw the differences between the various OAuth 2.0/OpenID Connect flows. In this one, we'll see how to reference the ASOS package and how to register it in the ASP.NET Core pipeline.
Referencing the OpenID Connect server middleware package
This post was updated to reflect the latest changes introduced in the 1.0.0 RTM version of ASOS.
To reference ASOS, simply add "AspNet.Security.OpenIdConnect.Server": "1.0.0" under the dependencies node of your .csproj file:
1 | <Project Sdk="Microsoft.NET.Sdk.Web"> |
Referencing the OAuth 2.0 validation middleware
You'll also need to add the validation middleware, in charge of verifying/decrypting the tokens produced by ASOS and protecting your API endpoints:
1 | <Project Sdk="Microsoft.NET.Sdk.Web"> |
The validation middleware is similar to the JWT bearer middleware developed by the ASP.NET team but was specifically designed to use the encrypted tokens issued by ASOS and to offer a much easier experience (it doesn't require any explicit configuration by default).
Starting with ASOS beta5, JWT is no longer the default format for access tokens, but is still supported natively. To use JWT tokens instead of opaque/encrypted tokens, follow the steps below:
- Remove the reference to
AspNet.Security.OAuth.Validationinproject.json. - Remove the validation middleware registration (
app.UseOAuthValidation()), - Reference the
Microsoft.AspNetCore.Authentication.JwtBearerpackage. - Register the JWT middleware using
app.UseJwtBearerAuthentication(). - Assign
options.AccessTokenHandler = new JwtSecurityTokenHandler()to override the default format.