Up-to-date samples for ASP.NET 4.x and OWIN can be found in the openiddict/openiddict-samples repository:
Last year, I announced that OpenIddict would become compatible with OWIN/Katana – and thus usable in any ASP.NET 4.x non-Core application – as part of the 3.0 release. While using OpenIddict in an OWIN application shouldn't be much different than using it in an ASP.NET Core application, there's actually a part than will slightly differ between the two platforms: dependency injection.
Globally introduced in ASP.NET Core 1.0, dependency injection support was not a thing in OWIN. Yet, OpenIddict itself depends on dependency injection for all its features: core, server and token validation. To work around the lack of official DI support, OpenIddict 3.0 will support two approaches: one working with the Autofac DI container and one without. This blog post briefly describes how to do that.
To keep things simple, we'll create a tiny self-hosted .NET 4.7.2 OWIN application, but of course, these 2 approaches also work in any ASP.NET application, no matter what's the host used: HttpListener, System.Web or even third-party options like Nowin.
For that, create a new application with the following .csproj, that contains the basic things we'll need: the Microsoft DI primitives used by OpenIddict, the OWIN self-host and hosting abstractions and the OpenIddict OWIN metapackage (that itself references the core, server and validation packages, plus the OWIN integration assembly):
1 | <Project Sdk="Microsoft.NET.Sdk"> |
Then, add the entry point...
1 | using System; |
... and the Startup class:
1 | using Owin; |
At this point, no matter the option you'll opt for, you'll need to instantiate a ServiceCollection and register the OpenIddict server and validation services (exactly like how you'd do in a ASP.NET Core application):
1 | public void Configuration(IAppBuilder app) |
If you read my previous post, you probably figured out that I used OpenIddict 3.0's degraded mode in this snippet to implement the OAuth 2.0 password flow, which allows using OpenIddict's server feature without any backing database.
If you try to run the project as-is, all you'll get is a 404 error, as there's still a thing we need to do: integrating OpenIddict into OWIN's request processing pipeline.
Using OpenIddict 3.0 with Autofac (recommended option)
Unlike most other DI containers, Autofac has an excellent OWIN integration story that keeps things very clean and well-integrated. To use Autofac with OWIN, reference the following packages:
1 | <PackageReference Include="Autofac.Owin" Version="5.0.1" /> |
Then, update your Configuration method to create the IContainer, import the ServiceCollection and register the Autofac OWIN middleware:
1 | public void Configuration(IAppBuilder app) |
This is the beauty of this option: nothing else is required.
Using OpenIddict 3.0 without Autofac
Without Autofac, things will get a bit more complicated, as you'll need to manage per-request scopes yourself. While we'll use the Microsoft DI container to achieve that, this approach is also doable with any other DI container that provides an IServiceProvider implementation.
For that, we'll have to add a middleware creating a service scope per request and injecting it in the OWIN environment with the System.IServiceProvider key (the value that the OpenIddict server and validation OWIN integrations expect). We'll also need to call app.UseOpenIddictServer() and app.UseOpenIddictValidation(), that register the OpenIddict OWIN authentication handlers.
1 | public void Configuration(IAppBuilder app) |
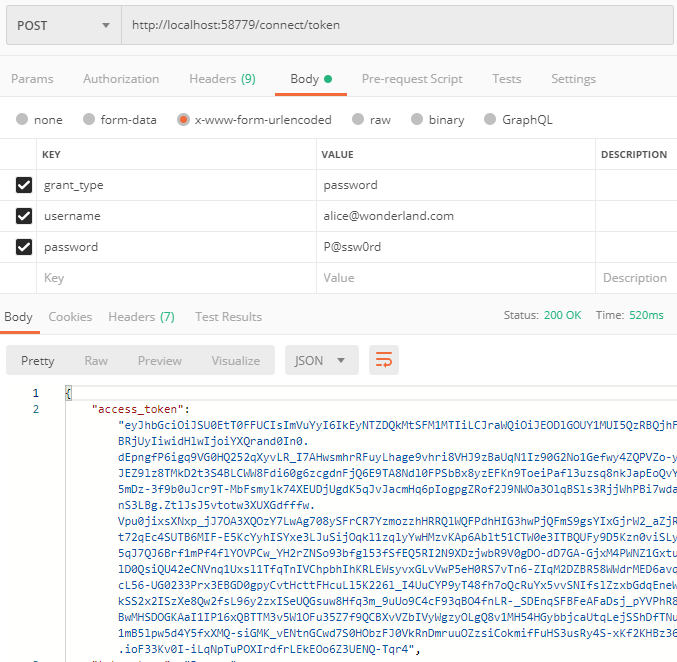
To ensure things are working properly, you can use Postman and send a token request:
Configure ASP.NET Web API to use token authentication (optional)
If your application uses ASP.NET Web API, a couple additional things will need to be configured:
- The OWIN host MUST be used to register the ASP.NET Web API integration. Concretely, this means you must ensure your application doesn't reference the
Microsoft.AspNet.WebApi.WebHostpackage. Instead, use theMicrosoft.AspNet.WebApi.Owinpackage and callapp.UseWebApi()at the end of yourStartup.Configuration(IAppBuilder app)method:
1 | public void Configuration(IAppBuilder app) |
When using Autofac and its ASP.NET Web API integration, you'll also need to call app.UseAutofacWebApi(configuration) before app.UseWebApi(configuration). For more information, read the Autofac documentation.
- To use token authentication for all Web API actions, the
HostAuthenticationFiltercan be registered globally to always call the OpenIddict validation handler:
1 | public void Configuration(IAppBuilder app) |
- Alternatively,
HostAuthenticationFiltercan be applied per-action or per-controller usingHostAuthenticationAttribute:
1 | [] |